NSA Open Sourcing Tools?
Reverse engineering never felt so easy
Recently I needed to reintroduce myself to decompiling firmware for embedded systems and was surprised at the range of tools available, especially the quality of open-source tools for such tasks. One tool stuck out among the rest and its story is really interesting.
On 7 March 2017, a series of documents began to get published on WikiLeaks and was called Vault 7. It details the activities and capabilities of the United States Central Intelligence Agency (CIA) to perform electronic surveillance and cyber warfare.
One of the software mentioned in those documents was Ghidra. It took two more years for the public to find out what it was. At the 2019 RSA Conference, the NSA showed its reverse engineering tool, the Ghidra. Soon after source code was posted on the official GitHub of NSA.
Wait, hold up, NSA, the windowless, cryptic, decryption agency has a GitHub account?
Today, Ghidra is a staple in college curriculums and is the subject of dozens of how-to books and videos. In 2020 Java Magazine listed it as one of the top 25 Java applications ever written. The Ghidra team has seen numerous examples of major technology and cybersecurity companies using Ghidra as part of their operations; others have created cybersecurity training using the Ghidra framework.
The technology has also been used to analyze consumer devices such as Wi-Fi routers, car electronics and voting machines. For example, New Hampshire used Ghidra in their forensic analysis of their 2020 State Representative contest.
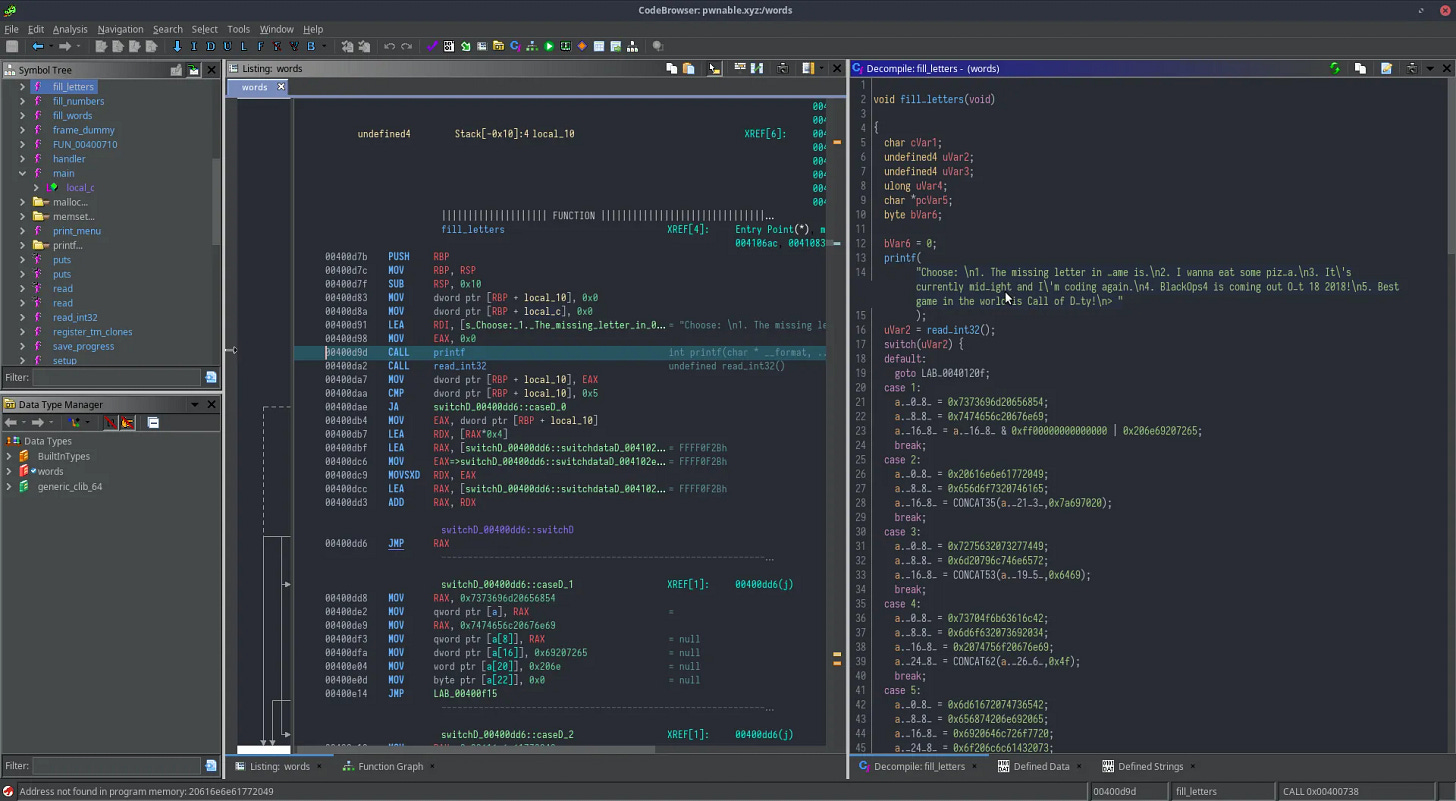
Ghidra is a free and open-source Interactive decompiler like Radare2. It includes a suite of software analysis tools that enable us to analyze compiled code. Up until 2019, IDA Pro was the industry standard when it comes to decompiling and debugging, and still is but it is losing ground to Ghidra at a fast pace as Ghidra is open source while IDA Pro is closed source and expensive (they now have free tier). Another commercial tool is binary.ninja.
A companion app to Ghidra for Windows is x64dbg, An open-source x64/x32 debugger. The difference between Ghidra and a tool such as x64dbg is that x64dbg is a debugger, meaning that it will run the target as you step through and analyze the code. While Ghidra since version 10.3 has an emulator ability that allows you to run code from any architecture supported without access to an environment with that architecture. There is a lot of overlap with dedicated debugging apps like x64dbg but since it does not actually run the code it is much safer to analyze malicious code. It does that by translating the executable to p-code which is then run in a portable code machine that executes the p-code on a hypothetical central processing unit (CPU). Pseudo-code for a pseudo-machine.
Ghidra's ability to emulate code for various architectures without requiring the actual hardware environment makes it exceptionally safe for analyzing potentially malicious code, as it doesn't execute the code directly on the host system. This feature, along with its decompilation and analysis capabilities, makes Ghidra a valuable tool for understanding and securing software. However, it can not replace true debuggers as it is limited to the implementation of such pseudo code/machine.
With regards to firmware of embedded systems one additional tool is a must, BinWalk. BinWalk can extract firmware images.
Today even a simple Hex Editor is impressive. ImHex is also an impressive open-source decompiler.
To test and learn how to crack software without doing anything illegal you can visit Crackmes.One which is a repository of reverse engineering puzzles. Another is pwnable.xyz.
My first foray into “decompiling” was around the 2000s. While in college we played a lot of Diablo II and Heroes of Might and Magic 2. I got frustrated at late late-stage gameplay of Heroes so I found where and how the game saved the game state, copied the save file, bought a couple of dragons, compared the new save file to the old one, and saw what changed. it was just a matter of increasing that to 255 so I could have a huge army of dragons. The game soon after became boring, well that’s the danger of it. It often starts as a challenge or a way to overcome a particularly tough part of a game, but ends up taking away the very essence of what made the game enjoyable in the first place.