Disseminating knowledge can be a double-edged sword. For the world to know how to protect itself from cyber threats one must tell the world how it’s done, in general terms, with pseudocode. On the one hand, it's critical to educate people about the tactics, techniques, and procedures used by malicious cyber actors to better protect themselves. On the other hand, this same information can potentially be used by malicious actors to refine their techniques and develop new strategies for exploitation.
MITRE ATT&CK (Adversarial Tactics, Techniques, and Common Knowledge) is a knowledge database that systematically documents tactics, techniques, and procedures used by penetration specialists as well as evil doers.
Developed by the non-profit organization MITRE Corporation, ATT&CK provides an extensive list of security threats and provides a reader with a comprehensive understanding of the cyber threat landscape, enabling them to proactively defend against potential attacks. But, knowledge is a double-edged sword.
ATT&CK matrix identifies and describes different adversary behaviors, like initial access methods, execution techniques, persistence mechanisms, privilege escalation techniques, defense evasion tactics, credential access methods, discovery behaviors, lateral movement techniques, collection methods, exfiltration techniques, and command and control protocols. Each behavior is thoroughly documented, with a description, examples, mitigation strategies, and detection methods.
It is an interesting read. Most of those techniques are obsolete but some are timeless, like phishing, or “having” a valid account. It was always easier to hack people than machines. There is also a directory of known hacking groups, which is really interesting and, at least to me even more interesting to read. In a sense, it reminds me of one of my favorite books, Approaching Zero: The Extraordinary Underworld of Hackers, Phreakers, Virus Writers, and Keyboard Criminals.
It's an old book now; the terminology is quaint both because it's targeted at the layperson and it almost predates the Internet. But it does form an important part of the limited literature available which covers that time period. Also, although it suggests that the doom and gloom scenario touted at the time with regards to technology destroying us all is over-hyped (as we can see in hindsight) the book still indulges in jumping on the hype bandwagon itself to some degree.
There is also a directory of Tools, of all sorts, commercial, open-source, and others. One thing I notice is that some tools are suspiciously missing, namely the Nmap variants like Netcat and Ncat which are extremely versatile and useful, especially in the early stages of network penetration testing. If combined with scripting language they are extremely “useful”.
In my post about
Embedded Security
I became interested in Default passwords at a really young age when BIOS passwords were popular for the protection of your computer. BIOS is a small piece of software that controls all of your computer components and is the first thing that is started up with a computer.
I covered the Internet Census of 2012 done by Carna Botnet that used Nmap Scripting Engine and discovered “an amazing number of open embedded devices on the Internet. Many of them are based on Linux and allow login to standard BusyBox with empty or default credentials.“ Here, “Amazing number” is understating the severity of the issue with hundreds of thousands of devices being compromised, in 2012!
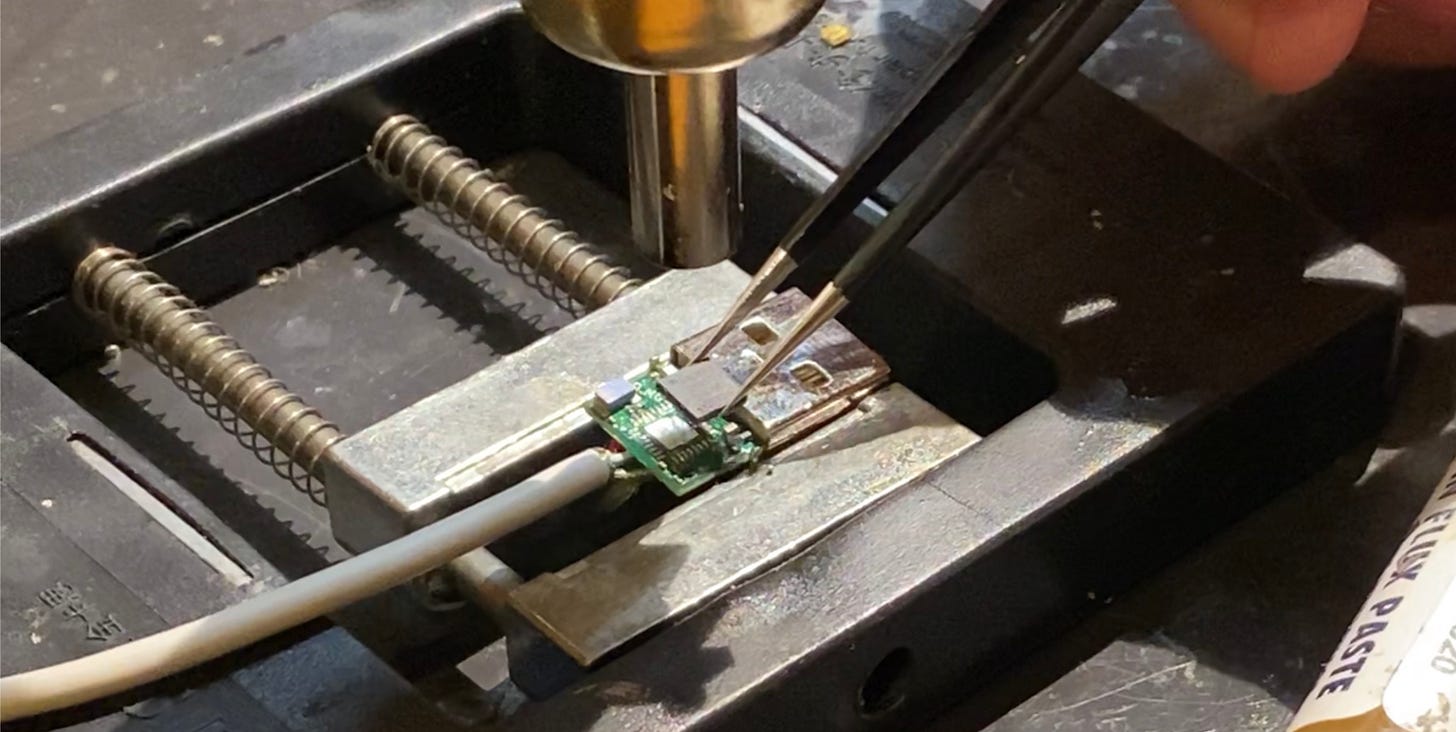
While there are references on the ATT&CK website about Nmap there is no information about it. The same is true about the Rubber Ducky while others are entirely missing. Tools like Flipper Zero and O.MG Cable can’t be found with a site’s search. They are currently the biggest threat to security than anything else as they are stealthy. Especially O.MG Cable which presents itself as an ordinary USB cable.
There is no information on what chip is used in O.MG Cable but going through the Official O.MG GitHub I found references to ESP8266, the older brother of ESP32. Most likely an SoC version like ESP8285H16 as it has 2MB of onboard Flash memory or ESP8266EX with external memory. There is no image of the back side of the PCB so there is no way to tell if there’s an external flash module there.
Overall the MITRE ATT&CK website is a good collection of everything dealing with cyber threats but either lacks regular updates or some of the most dangerous modern attack vectors have slipped by them making the site a good starting point and an interesting read but more for educational and historic purposes than actual current threats.